mirror of
https://github.com/dani-garcia/vaultwarden.git
synced 2026-03-22 12:45:23 -05:00
User type 'User' cannot share password with collection #77
Reference in New Issue
Block a user
Delete Branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @syserr0r on GitHub (Aug 28, 2018).
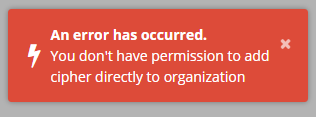
A user who has access to the collection (and not 'Readonly') cannot share a password with that collection -- when attempting to do so the following error is shown:
The only work-around is to set the user type to 'Admin' (or 'Owner'), however this allows access to all collections regardless of the explicit collection permissions
@syserr0r commented on GitHub (Aug 28, 2018):
The issue seems to be the
has_full_access()check here:781056152a/src/api/core/ciphers.rs (L140-L145)@mprasil commented on GitHub (Aug 28, 2018):
Yeah we seem to call the function from here:
781056152a/src/api/core/ciphers.rs (L425-L440)We do check the collection access later, so in this case we might need to somehow relay the information to the function we call, that user doesn't need write access to the entire organization as we will add it to collection later. (and maybe we should do that part first, that way if the collection stuff fails for whatever reason, we won't add the cipher to the organization direct for user that might not have the rights)
@durd commented on GitHub (Jul 22, 2019):
Sorry to reopen this, we are experiencing this issue aswell, albeit it with a different error but same meaning. I do get the same error when trying to remove the item from a collection, not sure if that is intended even if I have write access.
Edit: simple User in above case.
We are running 2.10.1 from docker bitwardenrs/server:latest on Debian 10.