mirror of
https://github.com/go-gitea/gitea.git
synced 2026-05-23 15:57:22 -05:00
Read/Push to a subtree limitation #1876
Closed
opened 2025-11-02 04:16:12 -06:00 by GiteaMirror
·
12 comments
No Branch/Tag Specified
main
release/v1.25
release/v1.24
release/v1.23
release/v1.22
release/v1.21
release/v1.20
release/v1.19
release/v1.18
release/v1.17
release/v1.16
release/v1.15
release/v1.14
release/v1.13
release/v1.12
release/v1.11
release/v1.10
release/v1.9
release/v1.8
v1.25.3
v1.25.2
v1.25.1
v1.25.0
v1.24.7
v1.25.0-rc0
v1.26.0-dev
v1.24.6
v1.24.5
v1.24.4
v1.24.3
v1.24.2
v1.24.1
v1.24.0
v1.23.8
v1.24.0-rc0
v1.25.0-dev
v1.23.7
v1.23.6
v1.23.5
v1.23.4
v1.23.3
v1.23.2
v1.23.1
v1.23.0
v1.23.0-rc0
v1.24.0-dev
v1.22.6
v1.22.5
v1.22.4
v1.22.3
v1.22.2
v1.22.1
v1.22.0
v1.23.0-dev
v1.22.0-rc1
v1.21.11
v1.22.0-rc0
v1.21.10
v1.21.9
v1.21.8
v1.21.7
v1.21.6
v1.21.5
v1.21.4
v1.21.3
v1.21.2
v1.20.6
v1.21.1
v1.21.0
v1.21.0-rc2
v1.21.0-rc1
v1.20.5
v1.22.0-dev
v1.21.0-rc0
v1.20.4
v1.20.3
v1.20.2
v1.20.1
v1.20.0
v1.19.4
v1.21.0-dev
v1.20.0-rc2
v1.20.0-rc1
v1.20.0-rc0
v1.19.3
v1.19.2
v1.19.1
v1.19.0
v1.19.0-rc1
v1.20.0-dev
v1.19.0-rc0
v1.18.5
v1.18.4
v1.18.3
v1.18.2
v1.18.1
v1.18.0
v1.17.4
v1.18.0-rc1
v1.19.0-dev
v1.18.0-rc0
v1.17.3
v1.17.2
v1.17.1
v1.17.0
v1.17.0-rc2
v1.16.9
v1.17.0-rc1
v1.18.0-dev
v1.16.8
v1.16.7
v1.16.6
v1.16.5
v1.16.4
v1.16.3
v1.16.2
v1.16.1
v1.16.0
v1.15.11
v1.17.0-dev
v1.16.0-rc1
v1.15.10
v1.15.9
v1.15.8
v1.15.7
v1.15.6
v1.15.5
v1.15.4
v1.15.3
v1.15.2
v1.15.1
v1.14.7
v1.15.0
v1.15.0-rc3
v1.14.6
v1.15.0-rc2
v1.14.5
v1.16.0-dev
v1.15.0-rc1
v1.14.4
v1.14.3
v1.14.2
v1.14.1
v1.14.0
v1.13.7
v1.14.0-rc2
v1.13.6
v1.13.5
v1.14.0-rc1
v1.15.0-dev
v1.13.4
v1.13.3
v1.13.2
v1.13.1
v1.13.0
v1.12.6
v1.13.0-rc2
v1.14.0-dev
v1.13.0-rc1
v1.12.5
v1.12.4
v1.12.3
v1.12.2
v1.12.1
v1.11.8
v1.12.0
v1.11.7
v1.12.0-rc2
v1.11.6
v1.12.0-rc1
v1.13.0-dev
v1.11.5
v1.11.4
v1.11.3
v1.10.6
v1.12.0-dev
v1.11.2
v1.10.5
v1.11.1
v1.10.4
v1.11.0
v1.11.0-rc2
v1.10.3
v1.11.0-rc1
v1.10.2
v1.10.1
v1.10.0
v1.9.6
v1.9.5
v1.10.0-rc2
v1.11.0-dev
v1.10.0-rc1
v1.9.4
v1.9.3
v1.9.2
v1.9.1
v1.9.0
v1.9.0-rc2
v1.10.0-dev
v1.9.0-rc1
v1.8.3
v1.8.2
v1.8.1
v1.8.0
v1.8.0-rc3
v1.7.6
v1.8.0-rc2
v1.7.5
v1.8.0-rc1
v1.9.0-dev
v1.7.4
v1.7.3
v1.7.2
v1.7.1
v1.7.0
v1.7.0-rc3
v1.6.4
v1.7.0-rc2
v1.6.3
v1.7.0-rc1
v1.7.0-dev
v1.6.2
v1.6.1
v1.6.0
v1.6.0-rc2
v1.5.3
v1.6.0-rc1
v1.6.0-dev
v1.5.2
v1.5.1
v1.5.0
v1.5.0-rc2
v1.5.0-rc1
v1.5.0-dev
v1.4.3
v1.4.2
v1.4.1
v1.4.0
v1.4.0-rc3
v1.4.0-rc2
v1.3.3
v1.4.0-rc1
v1.3.2
v1.3.1
v1.3.0
v1.3.0-rc2
v1.3.0-rc1
v1.2.3
v1.2.2
v1.2.1
v1.2.0
v1.2.0-rc3
v1.2.0-rc2
v1.1.4
v1.2.0-rc1
v1.1.3
v1.1.2
v1.1.1
v1.1.0
v1.0.2
v1.0.1
v1.0.0
v0.9.99
Labels
Clear labels
$20
$250
$50
$500
backport/done
💎 Bounty
docs-update-needed
good first issue
hacktoberfest
issue/bounty
issue/confirmed
issue/critical
issue/duplicate
issue/needs-feedback
issue/not-a-bug
issue/regression
issue/stale
issue/workaround
lgtm/need 2
modifies/api
modifies/translation
outdated/backport/v1.18
outdated/theme/markdown
outdated/theme/timetracker
performance/bigrepo
performance/cpu
performance/memory
performance/speed
pr/breaking
proposal/accepted
proposal/rejected
pr/wip
pull-request
reviewed/wontfix
💰 Rewarded
skip-changelog
status/blocked
topic/accessibility
topic/api
topic/authentication
topic/build
topic/code-linting
topic/commit-signing
topic/content-rendering
topic/deployment
topic/distribution
topic/federation
topic/gitea-actions
topic/issues
topic/lfs
topic/mobile
topic/moderation
topic/packages
topic/pr
topic/projects
topic/repo
topic/repo-migration
topic/security
topic/theme
topic/ui
topic/ui-interaction
topic/ux
topic/webhooks
topic/wiki
type/bug
type/deprecation
type/docs
type/enhancement
type/feature
type/miscellaneous
type/proposal
type/question
type/refactoring
type/summary
type/testing
type/upstream
Mirrored from GitHub Pull Request
Milestone
No items
No Milestone
Projects
Clear projects
No project
No Assignees
Notifications
Due Date
No due date set.
Dependencies
No dependencies set.
Reference: github-starred/gitea#1876
Reference in New Issue
Block a user
Blocking a user prevents them from interacting with repositories, such as opening or commenting on pull requests or issues. Learn more about blocking a user.
Delete Branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @publicocean0 on GitHub (Jun 6, 2018).
i gave a look at gitea it is very interesting . Anyway i saw maybe a functional limitation:
it is not possible to limit action for a developer in a specific subtree and branch
@axifive commented on GitHub (Jun 6, 2018):
This is already present in the repo settings:
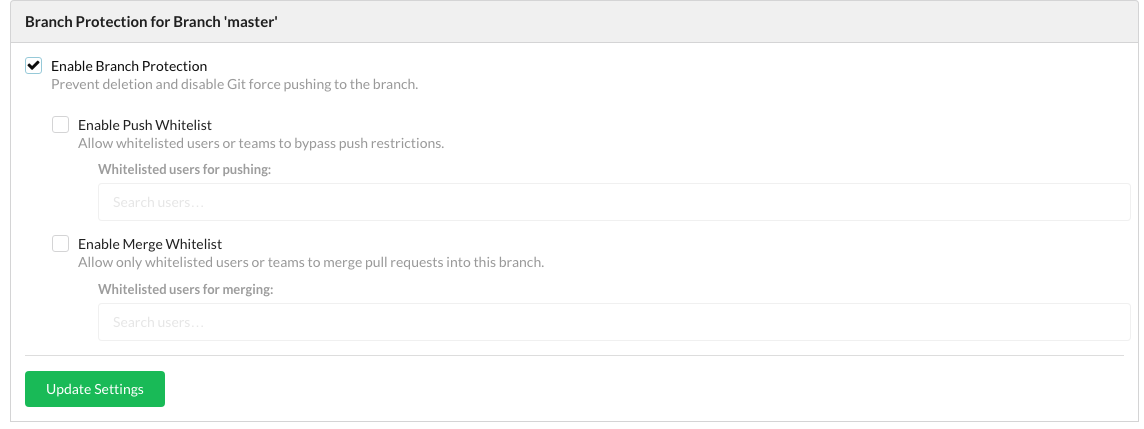
Settings => Branches => Branch Protection
@publicocean0 commented on GitHub (Jun 6, 2018):
if i want a collaborator cant see a branch? or cant read the entire project but just a subfolder where he can work in a specific branch?
@daviian commented on GitHub (Jun 6, 2018):
I would argue that hiding branches isn't possible because git itself doesn't provide that functionality.
Pushing to a subtree may be realizable although I don't see the real benefit.
Extracting that code into a separate component / repository may be a cleaner way to achieve this kind of functionality.
Furthermore if it is sufficient for the developer to only see a certain subtree / folder the code is already modular enough to separate them.
@markuman commented on GitHub (Jun 6, 2018):
I don't think git is working that way. A collaborator will always see any branches of a repository, but push access can be restricted to branches.
@publicocean0 commented on GitHub (Jun 6, 2018):
i m used to work with gitolite where it is possible
@lunny commented on GitHub (Jun 6, 2018):
Read/Push to a subtree limitation maybe a new feature. Don't know how gitolite did it.
@daviian commented on GitHub (Jun 6, 2018):
@publicocean0 Do you mean subtree of the files or a subtree of branches? Just that we are talking about the same thing ;-)
@publicocean0 commented on GitHub (Jun 6, 2018):
with gitolite you can decide where a developer can push, pull , read , write .
it is quite simple you create a regular expression about path in the project with associated permissions.
/ab/cd/a/* R dev1,dev2,dev3
/ac/rf/* RW dev4,dev5,...
/ar/u/RW+ dev6,dev7
....
@tfheen commented on GitHub (Apr 2, 2019):
My particular use case is that I have a repository where machines should be able to push to a particular file with their state in, but not otherwise change the state of that repository. They should also not be able to influence state from other machines. Doing the same thing with submodules and symlinks, while possible, would be a lot more work and hassle.
It is, as you note, not possible to restrict reading to subtrees due to how git works, but that's not a concern of mine, I'm only interested in limiting push.
I can see a few different ways to implement support for this, and would like some feedback on options:
I'm happy to spend some time on this, since I'd like to have the functionality, but would like the direction to be aligned with what you'll accept into the project. If you have other approaches you think would be viable and wanted, I'm of course happy to discuss those.
@zeripath commented on GitHub (Apr 5, 2019):
Ok you can do checking of push paths using a pre-receive hook. Admittedly the UI is not as nice as in gitolite but if you did want to move to Gitea it is possible.
@tfheen commented on GitHub (Apr 6, 2019):
You can, but it would be massively more useful if you actually had the deploy key which was used for pushing. I'd rather not create a real account for each and every one of my machines (IIRC, the account name of the pusher is exposed as a variable name, but not the key's name).
@zeripath commented on GitHub (Apr 6, 2019):
At present the way I fixed the deploy keys was to make them act as the owner of the repository - this is clearly not ideal. I guess I think sending the hooks the keyid is probably a reasonable half-way house.
If I had to say what the correct answer is - deploy keys are virtual users (acting as the owner but with additional parts to their name) and should be treated as such but that could be difficult to refactor in.
If we could create some kind of virtual user we could actually add true Become User functionality to Gitea with real auditable actions etc.